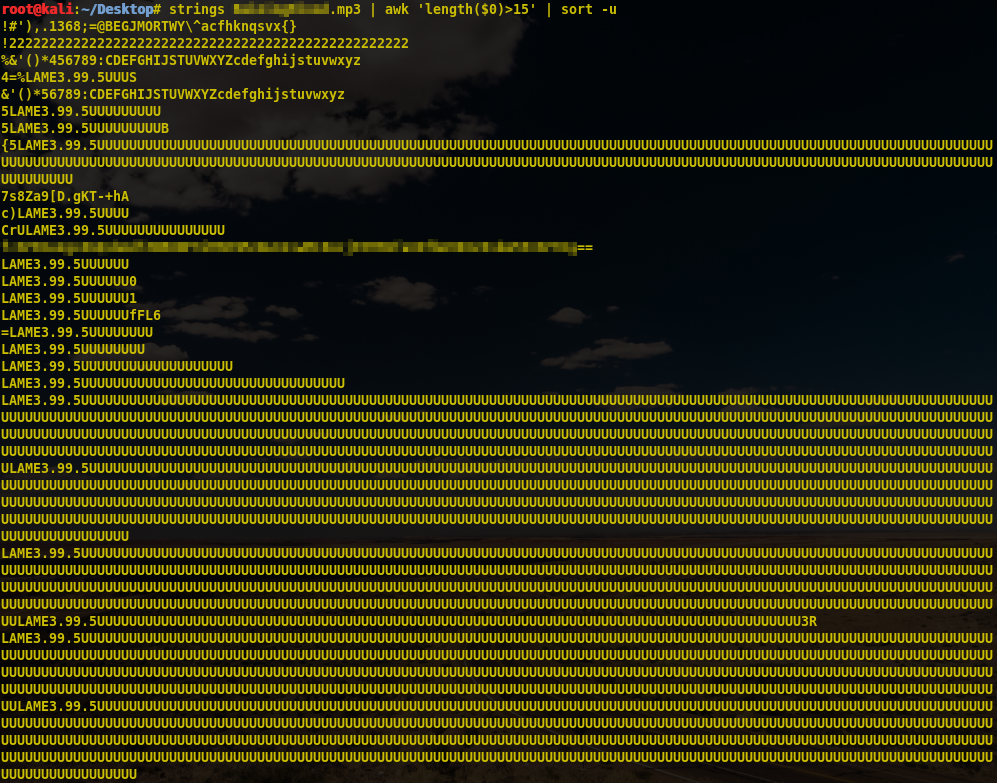
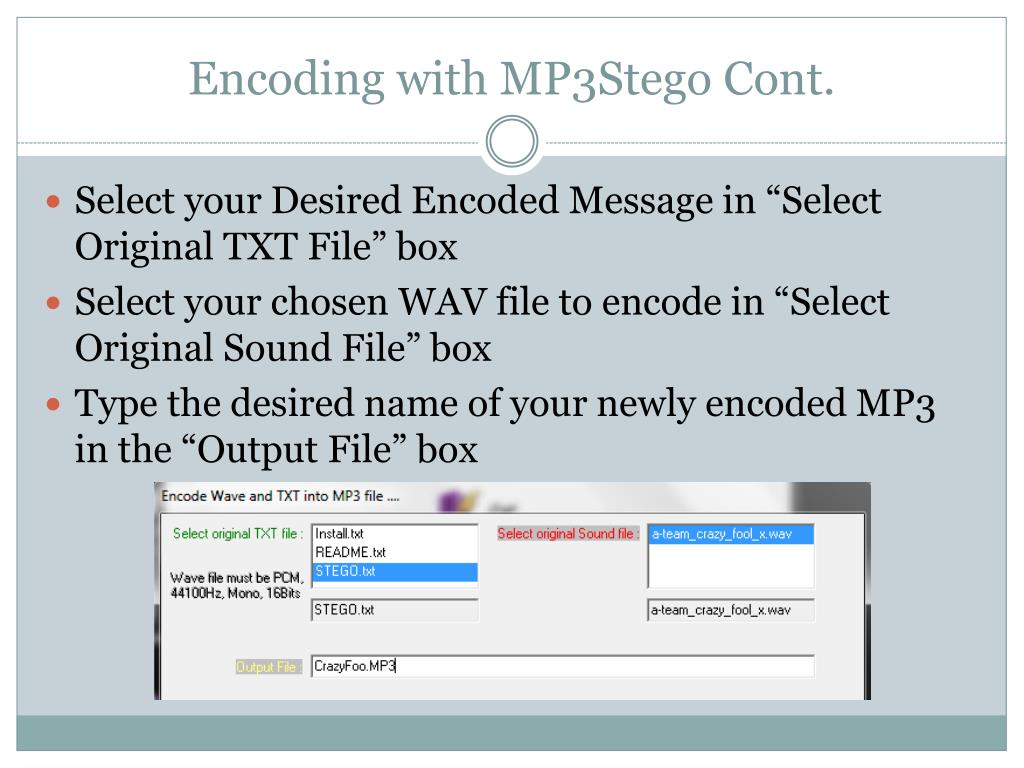
Increasing the security of mp3 steganography using AES Encryption and MD5 hash function | Semantic Scholar
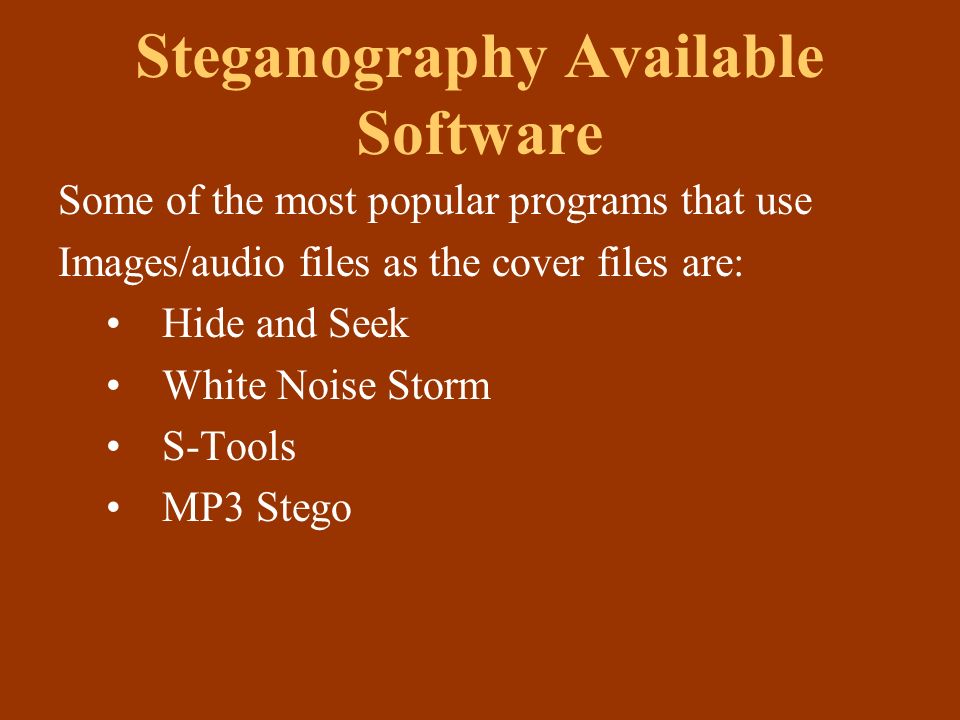
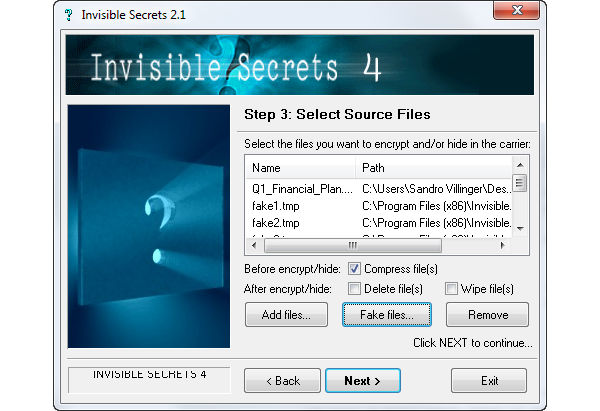
Steganography. Outline What is Steganography? History Steganography used nowadays? Terms Steganography methods Steganography Available Software Steganalysis. - ppt download
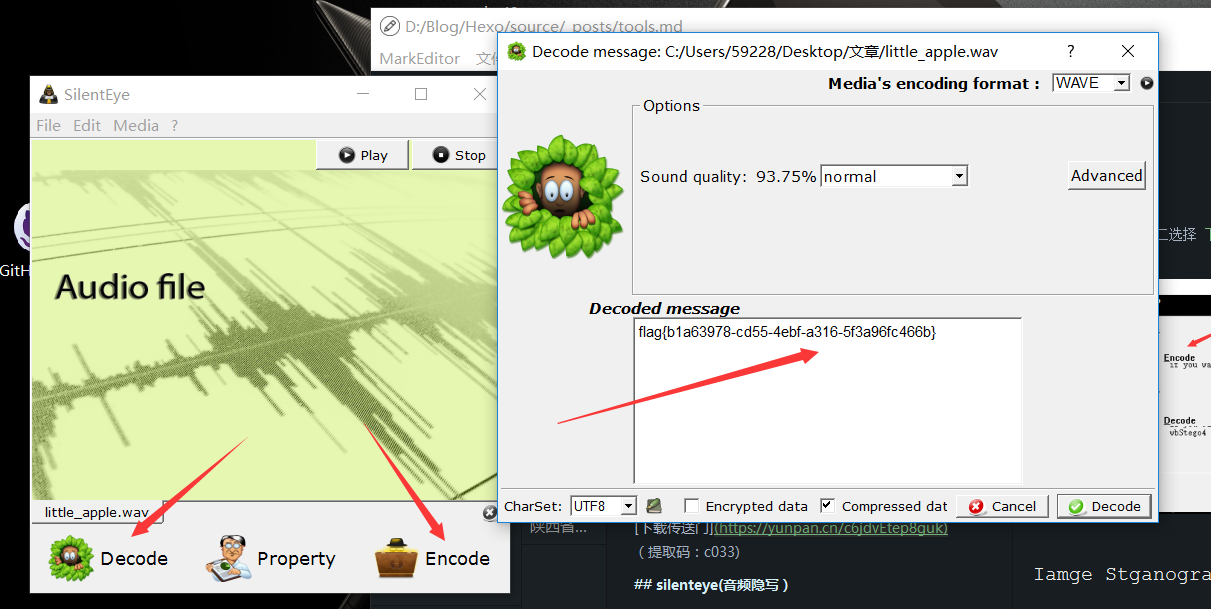
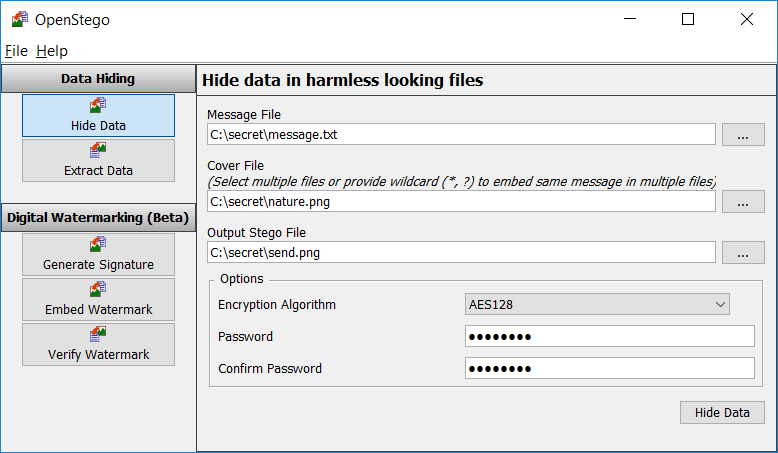
Audio Steganography via Cloud Services: Integrity Analysis of Hidden File - Document - Gale Academic OneFile




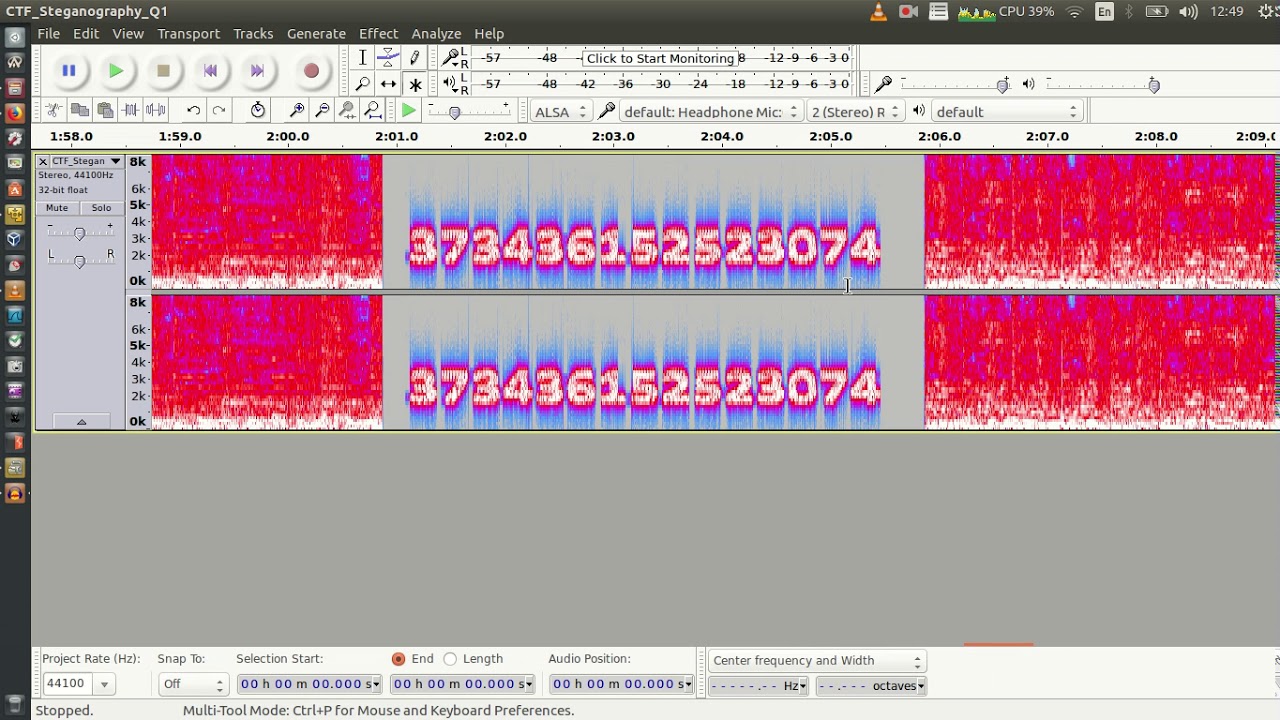
![Raining Blood [medium]: HackTheBox Stego Challenge (mp3 steganography) - YouTube Raining Blood [medium]: HackTheBox Stego Challenge (mp3 steganography) - YouTube](https://i.ytimg.com/vi/bosAgA4AKRU/maxresdefault.jpg)

![Raining Blood [medium]: HackTheBox Stego Challenge (mp3 steganography) - YouTube Raining Blood [medium]: HackTheBox Stego Challenge (mp3 steganography) - YouTube](https://i.ytimg.com/vi/WKNgPUx-OSw/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLDpM5LZYsgE3j9EusF1L2nT4P3sZg)